This newsletter is your one-stop, 360-degree useful resource protecting the entire data you want to find out about WAFs, together with how they serve as, what they offer protection to in opposition to, the right way to put into effect them, and a lot more!
Protective your internet programs in opposition to malicious safety assaults is very important. Happily, WAFs (Internet Software Firewalls) are right here to assist.
In a nutshell, a WAF works as a protect between the internet utility and the web, fighting mishaps that might happen with out it.
WAFs can offer protection to you and your purchasers’ programs from cross-site forgery assaults, XSS (cross-site-scripting), and SQL injections, among others.
An increasing number of so, internet utility safety has grow to be extra an important, bearing in mind internet utility assaults are probably the most commonplace causes for breaches.
As you’re about to look, WAFs are a crucial a part of safety to protect in opposition to vulnerabilities.
On this article, we’ll be protecting:
- What is a WAF?
- WAFs and Network Firewalls
- Differences Between Network-Based, Host-Based, and Cloud-Based WAFs
- How WAFs Protect Your Web Applications From Malicious Attacks
- WAFs Security Models: Blocklist, Allowlist, Or Both
- Attacks Prevented by WAFs
- How WAFs Guard Your Web Apps Against The “The OWASP Top 10”
- How WAFs Also Help You Meet Legal Security Standards
- Different Types of WordPress Firewalls
- Limitations of WordPress Firewalls
- WAF Deployment
- WAF Vendors
- Conclusion
Let’s get started initially, with…
Contents
- 1 What’s a WAF?
- 2 WAFs and Community Firewalls
- 3 Variations Between Community-Primarily based, Host-Primarily based, and Cloud-Primarily based WAFs
- 4 How WAFs Offer protection to Your Internet Packages From Malicious Assaults
- 5 WAF Safety Fashions: Blocklist, Allowlist, Or Each
- 6 Assaults Avoided by way of WAFs
- 7 How WAFs Guard Your Internet Apps In opposition to The “The OWASP Best 10”
- 8 How WAFs Additionally Assist You Meet Prison Safety Requirements
- 9 Other Varieties of WordPress Firewalls
- 10 Barriers of WordPress Firewalls
- 11 WAF Deployment
- 12 WAF Distributors
- 13 It’s No Gaffe That You Desire a WAF
What’s a WAF?
A Web Application Firewall (WAF) is a particular form of firewall that protects your internet programs from malicious application-based assaults.
In layman’s phrases, a WAF acts as the center particular person or safety guard to your WordPress website.
It’s going to assist offer protection to internet programs from assaults like cross-site scripting (XSS), cookie poisoning, SQL injection, cross-site forgery, and extra.
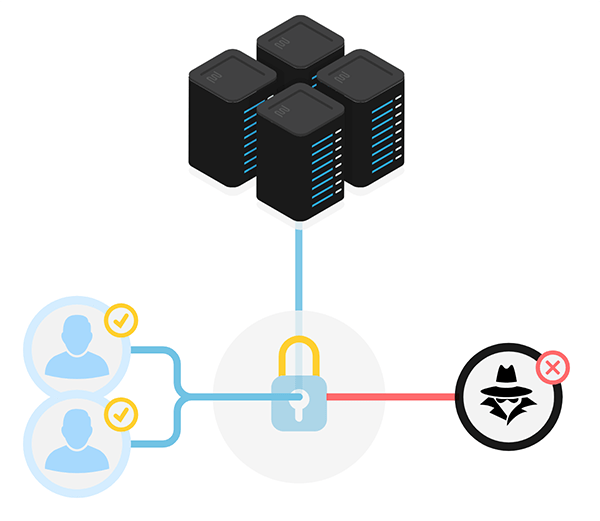
WAFs will stand guard between the web and your internet programs, the entire whilst tracking and filtering the HTTP site visitors that wishes to get on your server.
It does this by way of adhering to insurance policies that help in figuring out what site visitors is malicious and what site visitors isn’t. Very similar to how a proxy server acts as a mediator to give protection to the identification of a consumer, WAF purposes similarly — however in opposite.
It’s a opposite proxy, which acts as a go-between that protects the internet utility server from a conceivable malicious shopper.
WAFs use a algorithm (or insurance policies) to assist determine who’s in truth for your visitor listing and who’s simply taking a look to motive hassle.
WAFs must no longer be at a loss for words together with your usual Community Firewall (Packet Filtering), which assesses incoming knowledge in response to a collection of standards, together with IP addresses, packet sort, port numbers, and extra.
Community firewalls are k and nice at what they do. The one problem is that they don’t perceive HTTP, and because of this, can not discover particular assaults that concentrate on safety flaws in internet programs.
That’s the place WAFs save the day and will assist bolster your internet safety in tactics a Community Firewall can not. There are lots of layers to it.
And employing different security measures help you additional offer protection to the person layers.
The OSI Fashion
To grasp those layers, you want to know the OSI Model (Open Systems Interconnection Model).
The OSI type is a framework that divides the full structure of a community into seven other sections.
Each and every layer has its personal safety postures and mechanisms, and someone overly concerned about safety must understand how to discover and identify suitable safety strategies for every.
The seven community layers are as follows:
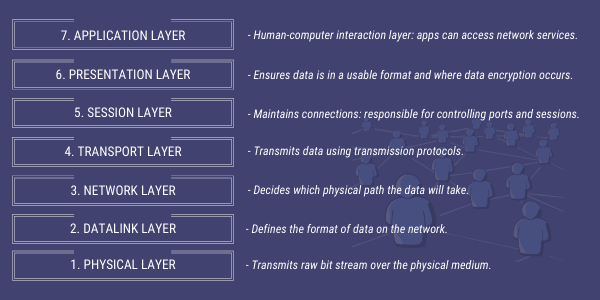
When inspecting the layers above, your standard Community Firewall is helping safe layers 3 – 4, and a WAF assists with the security of layer 7.
This must additionally function a reminder that WAFs are NOT a one-size-fits-all resolution. They usually’re highest paired with different fantastic security features – equivalent to a top quality Community Firewall.
Variations Between Community-Primarily based, Host-Primarily based, and Cloud-Primarily based WAFs
WAFs are utilized in one among 3 quite a lot of tactics — network-based, host-based, and cloud-based. Each and every has advantages and drawbacks, so let’s check out every one in my view and notice how they evaluate.
Community-Primarily based: Community-based WAFs are usually hardware-based. They’re put in in the neighborhood; subsequently they reduce latency. On the other hand, they’re a pricey choice that still calls for garage and upkeep of kit.
Host-Primarily based: In the case of prices, that is not up to network-based WAFs. Plus, it provides extra customization choices. One of the vital downsides of this sort of WAF is the intake of native server assets, upkeep prices, and it may be advanced to put into effect.
Cloud-Primarily based: That is an inexpensive choice — and it’s simple to put into effect. Generally, it’s only a topic of trade in DNS to redirect site visitors. Additionally, cloud-based WAFs have a low prematurely charge, with versatile cost choices. Those WAFs are persistently up to date to assist offer protection to in opposition to the most recent threats that stand up that received’t require any paintings or bills at the person’s facet.
Almost certainly the most important problem of this sort of WAF is it’s from a third birthday party supply, so you might be restricted to customization choices and depend only on their services and products.
Now that we have got a elementary thought of what a WAF is and the differing kinds, let’s dive deeper into HOW it protects your valuable internet apps.
How WAFs Offer protection to Your Internet Packages From Malicious Assaults
In keeping with a 2019 web applications report by Positive technologies, on reasonable, hackers can assault customers in 9 out of 10 internet programs. Yikes!
The file additionally discovered that breaches of delicate knowledge have been a danger in 68% of internet programs.
Statistics like those enhance the desire for simpler internet app coverage.
As discussed previous, WAFs offer protection to your server by way of inspecting the HTTP site visitors passing thru – detecting and blocking off the rest malicious BEFORE it reaches your internet programs (see beneath).
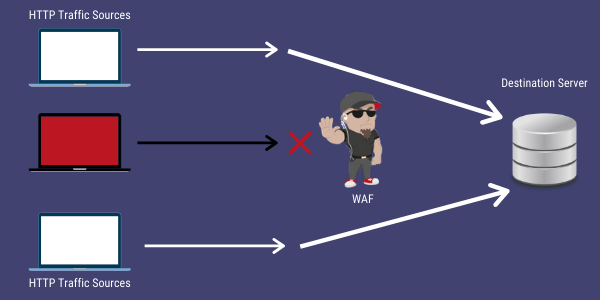
As we simply mentioned, WAFs can be community ({hardware}) founded, software-based, or cloud-based, which means digital or bodily.
In the case of how WAFs clear out, discover, and block malicious site visitors – they do so in a few other ways…
WAF Safety Fashions: Blocklist, Allowlist, Or Each
WAFs usually apply both a “Blocklist” (destructive) or “Allowlist” (sure) safety type, or from time to time each.
When using a Blocklist safety type, mainly, you’ll collect a listing of undesirable IP addresses or person brokers that your WAF will robotically block.
The Allowlist type does the other and lets you create an unique listing of IP addresses and person brokers which might be accepted. The entirety else is denied.
Each fashions have their execs and cons, so fashionable WAFs ceaselessly be offering a hybrid safety type that provides you with get right of entry to to each.
Assaults Avoided by way of WAFs
Clearly, no longer each and every assault available in the market may also be stopped by way of a WAF, alternatively, they assist care for a large number of them.
Probably the most main assaults that WAF safety can assist give up are:
SQL Injection: That is malicious code this is injected or inserted right into a internet access box. The injections permit assaults to compromise the applying and in addition underlying techniques.
Pass-site Scripting (XSS): Consumer-side scripts are injected by way of attackers into internet pages different customers view.
Internet Scraping: Used to extract knowledge from internet sites by way of knowledge scraping.
Unvalidated Enter: HTTP requests are tampered with by way of attackers to avoid safety mechanisms on a website.
Cookie Poisoning: When a cookie is changed to achieve unauthorized information concerning the person for malicious functions, equivalent to identification robbery.
Layer 7 DoS: HTTP flood assault that uses legitimate requests in standard URL knowledge.
Safety improvements are repeatedly being up to date and applied, so take into account a just right WAF can duvet much more than simply famous above.
When figuring out a WAF supplier, or imposing one, ensure that it’s up-to-date and comprises the necessities, particularly the OWASP Best 10 — which we’ll be discussing subsequent.
How WAFs Guard Your Internet Apps In opposition to The “The OWASP Best 10”

In addition to acting in response to one of the crucial 3 safety fashions discussed previous, WAFs come robotically armed with a particular algorithm (or insurance policies).
Those insurance policies mix rule-based common sense, parsing, and signatures to assist discover and save you many alternative internet utility assaults like up to now discussed.
Particularly, WAFs are widely known for shielding in opposition to quite a few the top 10 web application security risks indexed yearly by way of OWASP (Open Internet Software Safety Mission).
This comprises malicious assaults equivalent to Server-Facet Request Forgery (SSRF), Injections, and Safety Logging.
Right here’s a take a look at the present Best 10. You’ll be able to see that there’s some consolidation and new classes from 2017.
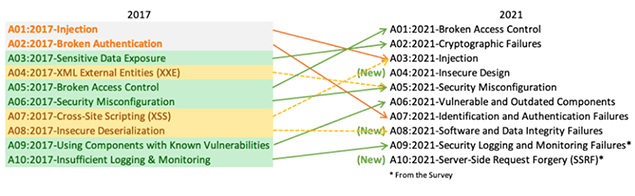
To find extra details about OWASP here.
Digital Patch
Any other good enough safeguard you’ll pay attention many WAF suppliers speak about is one thing referred to as a “digital patch.”
A VP is largely a rule (or ceaselessly a algorithm) that may assist resolve a vulnerability in your software while not having to regulate the code itself.
Many WAFs can deploy digital patches to fix WordPress core, plugin, and theme vulnerabilities when required.
How WAFs Additionally Assist You Meet Prison Safety Requirements
Together with safety, a WAF can assist with legalities.
If your company works with, processes, or retail outlets delicate data (bank card main points, and so on.), it’s crucial you agree to safety necessities and requirements. That is the place a WAF comes into play.
WAFs can assist companies of all sizes agree to regulatory requirements just like the PCI, HIPAA, and GDPR, making the firewall precious from compliance and safety views.
For instance, the #1 requirement for organizations beneath the Payment Card Industry Data Security Standard (PCI) is: “Putting in and keeping up a firewall configuration to give protection to cardholder knowledge.”
And let’s face it, retaining in compliance with legalities additionally provides you with an excellent popularity. It’s a win-win to make use of a WAF to fulfill criminal requirements.
Other Varieties of WordPress Firewalls
Taking into account WordPress is the arena’s hottest content material supervisor and a widespread goal of assaults, it’s necessary WordPress websites have a WAF in position. There are various kinds of firewalls varieties you’ll deploy, that are:
- WAF Safety Plugins
- On-site Devoted WordPress WAFs
- On-line WordPress Web site WAFs
Right here’s a take a look at every one.
WAF Safety Plugins
Maximum self-hosted WordPress firewalls are WordPress plugins. They’re splendid, bearing in mind how simple they’re to put into effect and inexpensive. Plus, it’s commonplace for the WAF plugins to have malware scanners, too.
Some apply a “SAAS” type, providing a very simple and enjoyable advent to the arena of utility firewalls.
At the different facet of the coin, some plugins received’t are compatible the invoice. It’s all dependent at the point at which the WAF sits.
For instance, some plugin WAFs sit down on the DNS point, which most often way the firewall displays and filters HTTP site visitors ahead of attaining their cloud proxy servers.
That is the beneficial point for a lot of these firewall plugins. Some well known WAF suppliers are arrange on this approach (e.g. Cloudflare — which is likely one of the suppliers we’ll be discussing later on this article).
Then you’ve different WordPress security plugins with integrated WAFs that sit down on the utility point. This implies the firewall examines incoming site visitors after it has already reached your server – however ahead of loading WordPress scripts.
Plugins are a easy and fantastic approach to WAF and most often paintings for small or medium-sized internet sites. We’ll be going over some choices of WAF distributors in a while on this article.
On-site Devoted WordPress WAFs
Most of these firewalls are put in between your WordPress websites and an web connection. Because of this each and every HTTP request despatched on your WordPress website to start with passes throughout the WAF.
Internet utility WAFs are slightly extra safe opinion than plugins. That being stated, they’re dearer and would require some technical wisdom to regulate.
On-line WordPress Firewalls
This kind of firewall does no longer want to be put in at the identical community as your webserver to serve as. It’s an internet provider that works like a proxy server, the place your website’s site visitors comes thru it for filtering and is then forwarded on your web site.
With an internet WordPress firewall, your website’s area’s DNS data will want to be configured to indicate to the net WAF. So, this involves your WordPress guests speaking with the net WordPress firewall, no longer exactly together with your WordPress web site.
The disadvantage? Your internet server must be available over the web for the WAF to ahead site visitors on your web site. In different phrases, other folks can proceed to be in contact immediately together with your internet server if the IP cope with is understood.
Mainly, in a non-targeted WordPress assault, by which attackers scan complete networks for prone websites, your internet server and website will nonetheless be reachable.
Happily, you’ll configure your server’s firewall to just reply to site visitors coming from the net WordPress firewall, so if this assault occurs, you received’t be a sufferer.
Barriers of WordPress Firewalls
Like the rest, firewalls may also be imperfect. Certain, they provide added coverage, however there are some vulnerabilities.
A few examples of this are Restricted 0-Day Vulnerability Coverage, and Internet Software Firewall Bypasses.
With the zero-day WordPress vulnerability, there’s doable that your WordPress firewall received’t block an assault.
For this reason your supplier responsive menu is significant. Plus, you must at all times use utility from responsive and relied on companies to verify the firewall regulations are up to date.
Relating to internet utility firewall bypasses, it’s only a topic of them having vulnerabilities. There are tactics available in the market about bypassing the security of WAFs.
Right here once more, in case your supplier is responsive and will remediate problems in a handy guide a rough period of time, you must be k.
It’s additionally no longer unusual for WAFs to have false positives (the place they block risk free site visitors) and false negatives (letting destructive site visitors thru). It’s because the applying is secure by way of WAF adjustments steadily.
Moreover, some safety protocols are ceaselessly unnoticed. This comprises preventative measures, equivalent to code and infrastructure audits no longer being taken.
There’ll at all times be new WAF vulnerabilities that stand up as new virtual gear emerge. Many safety problems get resolved, however some aren’t spotted straight away.
All this being stated, WAFs want to be actively maintained and configured to verify they’re up-to-date.
WAF Deployment
WAFs are deployed in a couple of tactics. This all depends upon the place your programs are deployed, what services and products are wanted, how you need them controlled, and the extent of flexibleness and function required.
Right here’s the short rundown…
Opposite Proxy: The WAF is a proxy to the applying server, so software site visitors heads immediately to the WAF.
Clear Opposite Proxy: This can be a opposite proxy with clear mode. On account of this, the WAF one at a time sends filtered site visitors to internet programs, which permits for IP protecting by way of having the cope with of the applying server hidden.
Clear Bridge: That is the place HTTP site visitors is going instantly to the internet utility. The result’s the WAF is clear between the software and the server.
You’ll must make a decision what means of deployment works highest and covers all that you want.
WAF Distributors
In the case of imposing WAFs, there’s no scarcity of businesses and distributors which might be available in the market to assist. Simply google “WAF Distributors” — and a ton of effects will seem, together with a large number of Best 10 lists and extra.
That being stated, here’s a take a look at one of the height firms available in the market that experience caught out to us as main contenders in relation to WAFs. All of them have options that cater to particular person wishes.
We’ll check out the next WAF distributors:
- AWS
- Cloudflare
- Azure
- WPMU DEV
- Imperva
- Prophaze
- Akamai
- Wordfence
- Sucuri
There’s a abstract of who they’re and what they’re highest at. Plus, we’ll indicate one of the height options of every corporate and the numerous preventative security features they deal with.
AWS

Amazon’s AWS WAF is helping give up assaults from internet exploits and bots that may modify availability, have an effect on your safety, and devour a ton of assets.
With this WAF, you’ll be in regulate of the way site visitors reaches your programs by way of putting in place safety regulations that run bot site visitors and block commonplace assault patterns (e.g. SQL Injections).
This WAF is deployed on Amazon CloudFront as a part of your CDN. What’s particularly beautiful about this WAF is that you just pay just for what you utilize, and the prices are in response to the choice of regulations you’ve. Plus, there are prices related to the choice of internet requests your utility receives.
Best Options: Amazon’s AWS WAF comprises its cost-effective internet utility coverage. Together with that, it has an ease of deployment and upkeep. Safety may be built-in relying on the way you expand your programs, providing you with extra customization choices than different WAFs.
Highest For: Companies of all sizes, so long as they’re AWS purchasers.
Is helping Mitigate: DDoS assaults, SQL Injections, and Pass-Web page Scripting (XSS).
Cloudflare
Cloudflare is a top-rated cloud-delivered utility safety corporate. And, in fact, a formidable WAF is built-in with its coverage. Their WAF blocks over 57 billion cyber threats in line with day.
Its world 100 Tbps community sees 30M requests in line with 2nd, so it’s up for the task in relation to dealing with your internet sites. It provides entire utility safety from the similar cloud community, making it sensible and uniform in relation to safety posture.
Cloudflare’s community has remarkable visibility into threats, which yields the sharpest and best gadget studying.
Best Options: It has layered defenses, together with Cloudfare controlled regulations, that supply complicated zero-day vulnerability protections. Plus, it makes use of the core OWASP regulations, makes use of customized rulesets, displays & blocks stolen or uncovered credentials, and has versatile reaction choices.
Moreover, it has logging & reporting, factor monitoring, analytics, and application-layer regulate.
Highest For: Non-public use to small and mid-sized companies. Additionally, it’s superb for high-level enterprises and firms. Plus, it has WordPress WAF regulations, so it’s nice for WordPress websites.
Is helping Mitigate: OWASP Best 10, Remark Junk mail, DDoS assaults, SQL injections, HTTP Headers, and extra.
Azure

Microsoft’s Azure is a cloud-native WAF that is likely one of the maximum a success cloud platforms available in the market.
The Azure provider provides a spread of utility that offer utilities to different techniques, and one of the crucial merchandise is the WAF. It tracks for the highest ten vulnerabilities logged by way of OWASP, and you’ll upload customized regulations, too.
It has a metered price price, calculated on an hourly price and information throughput price — then charged per thirty days. This offers a lot decrease prematurely prices in comparison to a couple different WAF suppliers.
Best Options: Azure has complete coverage for OWASP, real-time visibility into your atmosphere, and safety indicators. Plus, it has complete REST API beef up in order that it may well automate DevOps processes. It additionally has DDoS coverage.
Highest For: Primary and small companies, alike.
Is helping Mitigate: OWASP Best 10, DDos Assaults, and any customized regulations (and extra).
WPMU DEV

We couldn’t let this text move by way of with out citing our very own highly optimized WAF right here at WPMU DEV. Our WAF is totally unfastened to make use of with our internet hosting, already tweaked for WordPress, up to date day-to-day, and a lot more.
The WAF we use makes use of fewer server assets by way of no longer working in PHP. Moreover, it doesn’t want to use a line of code, so your website’s efficiency will stay robust.
We even have over 300+ firewall regulations (or insurance policies). Those insurance policies mix rule-based common sense, parsing, and signatures — which permits them to discover and prevent internet utility assaults.
See the right way to put into effect our WAF in this article.
Best Options: After checking out, our WAF is 25% quicker than main plugin-based firewall. On height of our 300+ firewall ruleset, we additionally offer protection to in opposition to the OWASP Best Ten. Moreover, it’s unfastened with any hosted account!
Highest For: Small to main WordPress websites, internet hosting resellers, and any company or person who manages more than one internet sites.
Is helping Mitigate: Assaults starting from SQL injections, XSS, and plenty of extra.
Imperva

Imperva’s WAF stops assaults with almost 0 mistakes in relation to false positives. It additionally has an international SOC to ensure your corporate is secure inside moments of discovery.
It’s an all-in-one safety resolution that has the entire options required for web site safety. There are unfastened gear for Knowledge Classification and Database Vulnerability Trying out.
Best Options: Imperva options safe cloud and on-premises programs. It stops OWASP Best 10 and Automatic Best 20, plus has assault detection, SIEM integration, and reporting.
Highest For: Small to large-sized firms.
Is helping Mitigate: OWASP Best 10 and Automatic Best 20 and extra.
Prophaze

Prophaze WAF handles a ton in relation to safety. No longer best is it a WAF, however it’s additionally a mixture of RASP, CDN, DDoS, and extra.
It provides real-time web site coverage by way of imposing tough cloud-based applied sciences that paintings in opposition to the newest threats. It robotically scans your website for 1000’s of vulnerabilities and the OWASP Best 10. On height of that, it doesn’t want any further configurations and automated updates to take on new threats.
Prophaze has limitless rule units. Plus, customized integrations with SIEM Answers and helps all public clouds (e.g. AWS).
Best Options: Some key safety features are Bot Migration, Actual-Time Dashboard, 24-7 beef up, and ML Primarily based Danger Intelligence.
Highest For: A variety from midmarket to excessive point undertaking.
Is helping Mitigate: OWASP Best 10 API, DDoS, Bot Coverage, and extra.
Akamai

Akamai’s WAF is a unswerving resolution that can offer protection to your website in opposition to all identified assaults. Its an international chief in DDoS, plus integrates entire DDoS coverage with its WAF. That makes it so that you received’t want to have site visitors routed thru two firms to obtain sure requests on your internet server.
With Akamai, discover threats with crowdsourced intelligence. Plus, deploy and arrange successfully with only some clicks.
Best Options: Akamai has extra automation than many different choices. It’s additionally simple to make use of with coverage in opposition to DDoS assaults and extra. It additionally includes a dashboard, indicators, and further details about blocked assaults and the way your website was once secure.
Highest For: Small to Huge Firms
Is helping Mitigate: DDoS Assaults and all OWASP Best 10.
Wordfence

Wordfence is any other forged choice for a WAF that’s made for WordPress websites as a well-liked all-in-one safety plugin with over two million energetic installs. It comprises an endpoint firewall and malware scanner that was once in particular constructed for WordPress.
Its WAF runs on the endpoint, which allows deep integration with WordPress, which is other than cloud choices because it doesn’t wreck encryption, can’t be bypassed, and will’t leak knowledge.
It additionally comes with a pleasing dashboard that signifies safety threats, scans, and extra.
Best Options: Junk mail clear out, scheduled safety scans, brute power assault prevention, reside site visitors tracking, and extra.
Highest For: WordPress websites and small to giant firms.
Is helping Mitigate: Brute power assaults, OWASP Best 10, and different malicious assaults.
Sucuri

Sucuri is a number one safety corporate for WordPress. It includes a cloud-based WAF that’s persistently up to date to fortify detection and mitigation in opposition to new and evolving threats. Plus, you’ll upload your personal customized regulations.
With Sucuri, you’ll additionally toughen your WordPress’s efficiency. It options caching optimization, Analyst CDN, and web site acceleration.
Best Options: DNS Degree Firewall, malware & blocklist removing services and products, and brute power coverage.
Highest For: WordPress websites and firms/companies of any length.
Is helping Mitigate: All identified assaults (e.g. SQL injections, RCE, RFU, and so on.).
In fact, there are lots of extra choices available in the market as neatly. That is only a shortlist of a few extremely rated firms that may serve you neatly in relation to WAFs.
It’s No Gaffe That You Desire a WAF
Now that we’ve lined the spectrum of WAFs, in the event you didn’t know, you’ll see that they’re advisable for safety, compliance, popularity, and peace of thoughts. And confidently, you discovered extra about WAFs than you ever idea you may!
Plus, with the various distributors to supply a WAF, you’ll have one up and working in a question of moments. Whether or not you run a WordPress website or no longer — there’s a WAF for you.
With a bit of luck, this reference information has helped to reply to any questions you or your purchasers have about WAFs.
WordPress Developers