When you run a WordPress website, chances are you’ll pay attention to the many security risks that might threaten your online business. As an example, Far off Code Execution (RCE) assaults can exploit your web site vulnerabilities to thieve records, smash your content material, or take over your website altogether.
Thankfully, you’ll simply protect your website via working out the bits and bobs of this type of assault. With right kind wisdom, you’ll take the essential steps towards securing your web site towards RCE hacks.
On this submit, we’ll speak about RCE assaults and the way they may be able to hurt your web site. Then, we’ll speak about 5 tactics you’ll offer protection to your website, together with the use of a Internet Utility Firewall (WAF). Let’s dive proper in!
Contents
- 1 An Evaluate of Far off Execution Assaults
- 2 Learn how to Offer protection to your Website online Towards Far off Code Execution Assaults (5 Techniques)
- 3 2. Ensure that Your Tool Is Up-to-Date
- 4 3. Use Buffer Overflow Coverage
- 5 4. Prohibit Person Get admission to Permissions
- 6 5. Use Intrusion Detection Tool
- 7 Conclusion
An Evaluate of Far off Execution Assaults
RCE is a cyber-attack the place a hacker remotely executes code instructions on any person’s tool. Those assaults would possibly occur if the host unknowingly downloads malicious malware. Then, the hacker can set up data-stealing malware and deny get admission to to consumer recordsdata till the landlord will pay a ransom or mines cryptocurrency.
Moreover, as soon as an attacker has uncovered a vulnerability, they may be able to workout entire keep an eye on over your knowledge and tool. Your buyer records could also be compromised, chances are you’ll lose your web site recordsdata, and your recognition can also be destroyed eternally.
Additionally, RCE assaults are expanding, emerging from 7 to 27 percent of the most typical important vulnerabilities between 2019 and 2020. This building up is most probably because of the COVID-19 pandemic shifting many companies to a virtual-first environment.
Learn how to Offer protection to your Website online Towards Far off Code Execution Assaults (5 Techniques)
We’ve simply lined the hazards of RCE assaults. Now, let’s speak about 5 tactics to offer protection to your web site from them!
1. Set up a Internet Utility Firewall
A Web Application Firewall (WAF) is a superb prevention device that may offer protection to your website towards more than a few safety dangers, together with RCE assaults. It displays and filters HTTP site visitors to dam suspicious events from breaching your defenses. Necessarily, it acts as a buffer between your internet server and incoming traffic.
As an example, a device like Sucuri WAF can safeguard your website towards RCE assaults, speed up your loading times, or even building up your web site’s availability:
Along with protective your website towards RCE assaults, Sucuri can take away current malicious code to your website and save you DDoS attacks. Relying to your internet host, your hosting service may also include WAF coverage.
2. Ensure that Your Tool Is Up-to-Date
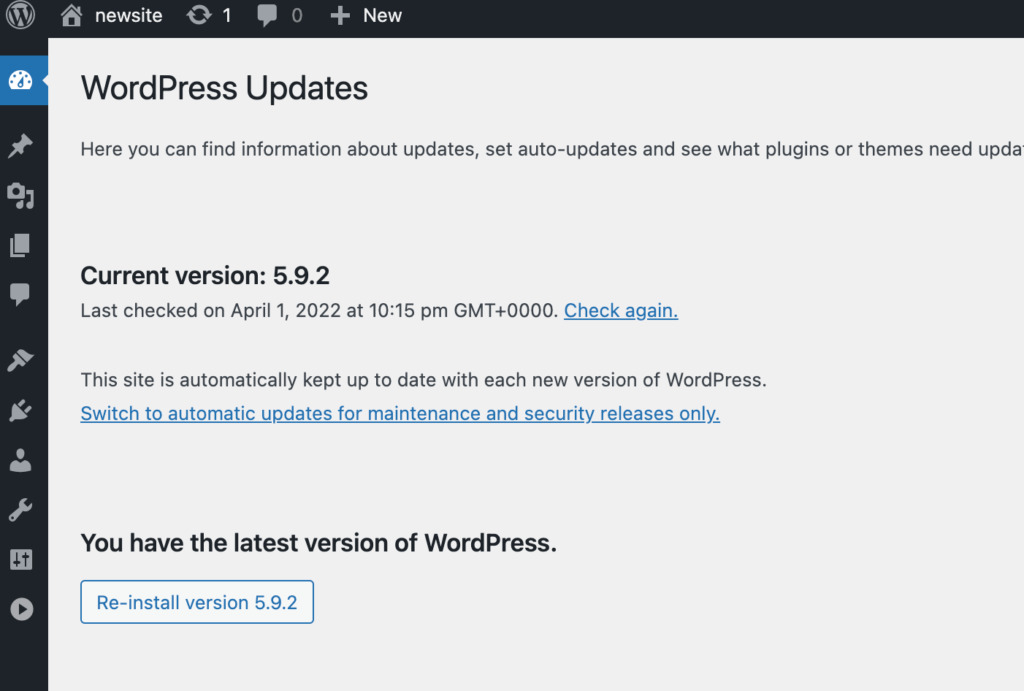
Holding all of your website software up-to-date is significant for RCE prevention. Subsequently, it’s the most important to constantly track your website for brand spanking new updates to topics, plugins, and the core WordPress tool.
The builders in the back of WordPress, plugins, and topics frequently roll out updates that make stronger safety and capability. Thus, updating your website as incessantly as conceivable successfully minimizes safety dangers that RCE hackers may exploit.
Head to Dashboard > Updates for your WordPress dashboard to manually replace your tool. Right here, you’ll view any to be had updates and allow them via clicking on them:
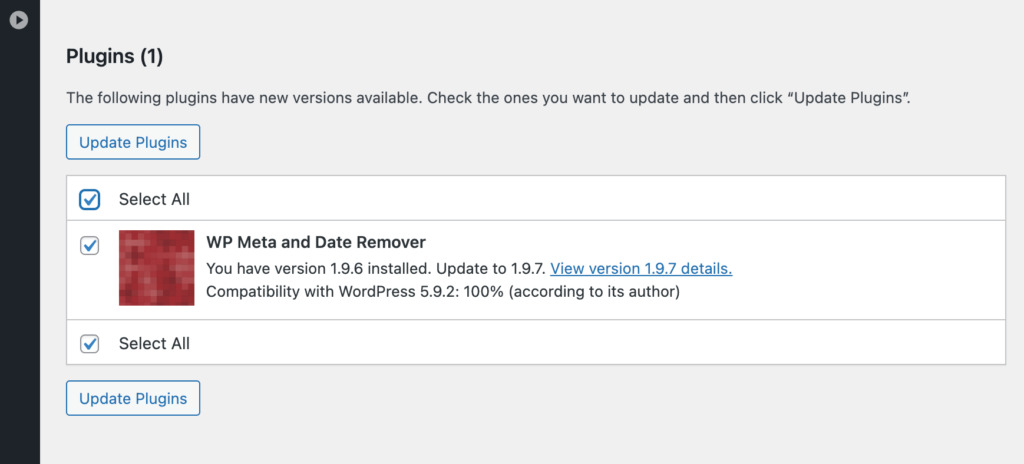
You probably have any old-fashioned plugins, click on on Make a choice All and Replace Plugins to get to the most recent variations:
However, you’ll spouse with a managed WordPress hosting provider. This corporate looks after more than one behind-the-scenes duties like computerized updates, web site safety, and function boosts. Opting for a controlled host can routinely offer protection to your website towards RCE assaults and different safety threats.
As an example, WP Engine is a competent internet host with a complicated WAF, computerized updates, day by day backups, and get admission to to each a Content Delivery Network (CDN) and SSL certification:
WP Engine internet hosting plans get started at $23 per month. This package deal helps one web site and 25,000 per thirty days guests.
3. Use Buffer Overflow Coverage
A buffer holds records in a reminiscence garage zone whilst it’s transferred between other places. Overflow occurs when the quantity of knowledge is greater than the buffer’s capability. When this occurs, the data-writing program begins overwriting different reminiscence places.
If there’s a buffer overflow, it may allow exploiters to overwrite your tool’s reminiscence. They are able to upload malicious code and dedicate an RCE assault. Subsequently, protective your website towards buffer overflow is significant to fighting RCE threats.
Thankfully, buffer overflow coverage is usually constructed into maximum theme code libraries in WordPress. Languages reminiscent of C/C++ would possibly not have buffer overflow coverage, however Javascript, PERL, and C# do.
Subsequently, we additionally suggest following coding best practices to offer protection to towards buffer overflow when growing your website.
4. Prohibit Person Get admission to Permissions
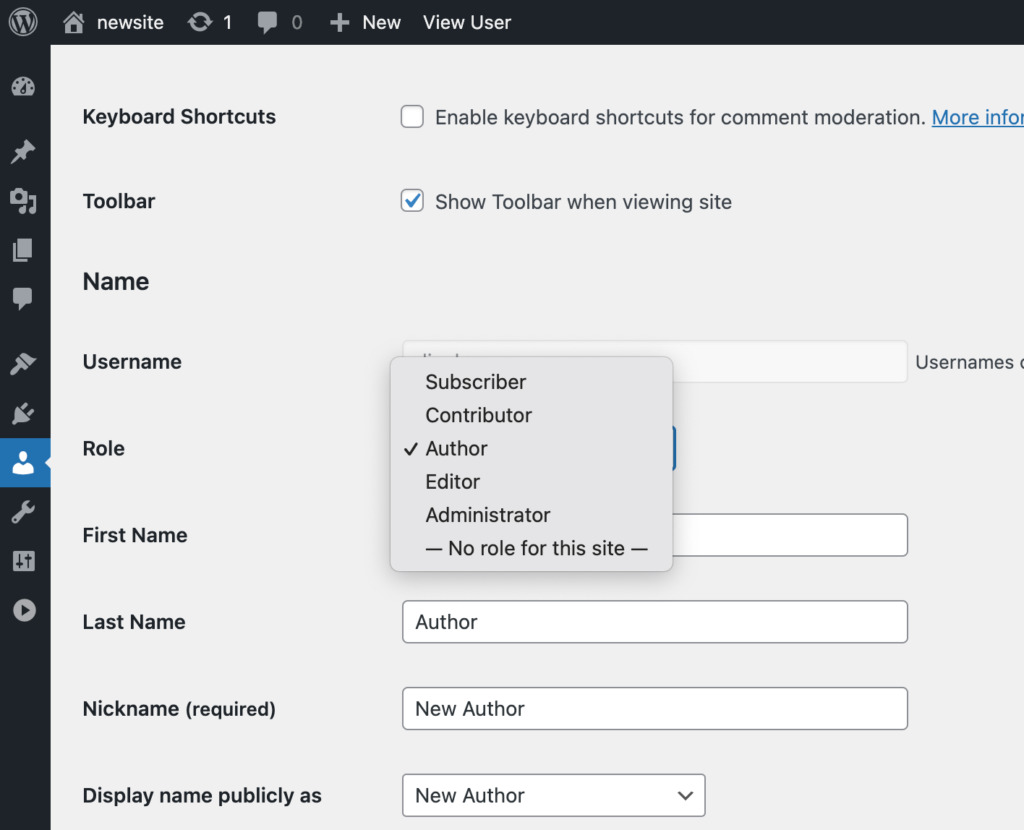
In WordPress, you’ll assign more than one other permissions in your customers. As an example, there are directors, editors, authors, members, and subscribers. Every consumer sort has other permissions, and most effective the administrator can immediately edit the code.
Via making sure every consumer most effective has the get admission to stage they want to do their task, your website gained’t be totally compromised if a hacker infiltrates one of the crucial consumer roles.
As an example, if in case you have freelance writers to your weblog, imagine assigning them as editors, authors, or members, relying on their roles.
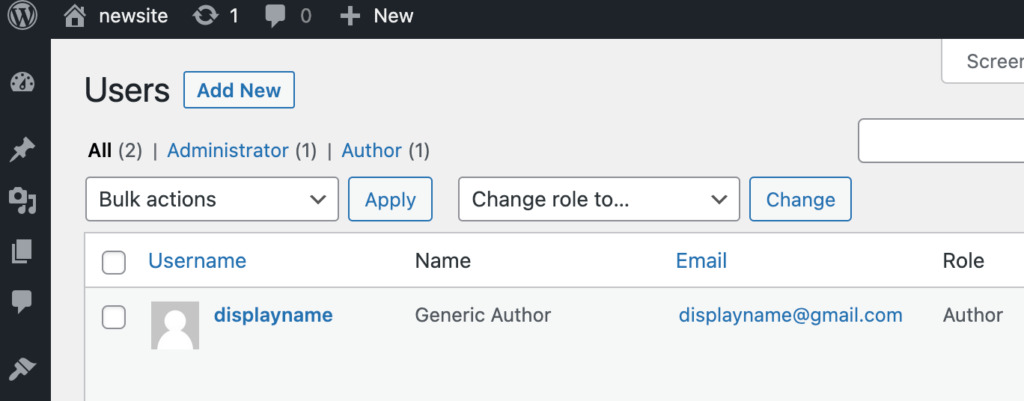
Navigate to Customers > All Customers for your WordPress dashboard to edit consumer roles. Then, click on on Edit beneath the consumer you wish to have to switch:
Then, scroll right down to Position and make a choice a suitable function for the consumer from the drop-down menu:
As a normal rule, don’t give any one the Administrator function except you wish to have them to have complete get admission to in your website and its code.
5. Use Intrusion Detection Tool
Intrusion Detection Tool (IDS) scans your web site’s inbound and outbound site visitors and notifies you if it detects suspicious task. With those notifications, you’ll know when and if you wish to have to take proactive measures towards RCE assaults.
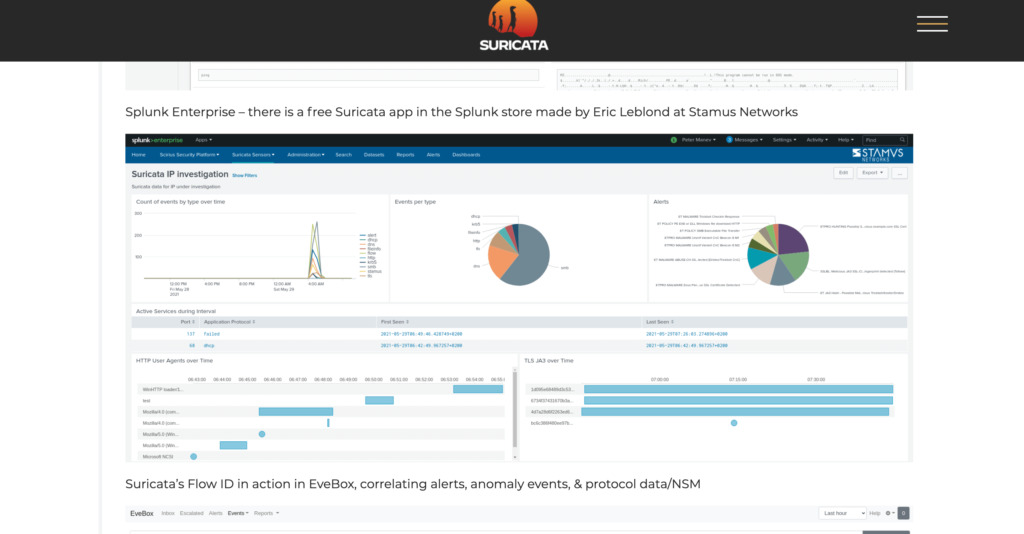
Suricata is an instance of a unfastened and open-source IDS device that may provide you with a warning when your community is receiving suspicious requests:
Along with intrusion detection, Suricata supplies services and products reminiscent of:
- TLS/SSL logging and research
- HTTP logging
- DNS logging
Suricata additionally supplies customers with a complete keep an eye on panel of analytics, occasions in keeping with sort, signals, and HTTP consumer brokers through the years.
Conclusion
Holding your safety up-to-date is an very important job as a WordPress website proprietor. If hackers can get admission to your website and thieve buyer records, you’ll most probably face serious felony and fiscal consequences. Alternatively, you’ll thwart not unusual cyber-attacks reminiscent of Far off Code Execution (RCE) via taking easy precautions.
On this submit, we mentioned 5 strategies for shielding your web site towards RCE assaults:
- Set up a Internet Utility Firewall (WAF).
- Ensure that your web site’s tool is up to date to cut back safety dangers.
- Ensure that your web site is safe towards buffer overflow.
- Prohibit your customers’ get admission to permissions.
- Make the most of Intrusion Detection Tool (IDS).
Do you could have to any extent further questions on Far off Code Execution assaults and the way to offer protection to towards them? Tell us within the feedback phase under!
The submit How to Protect Your Site Against Remote Code Execution Attacks (5 Ways) gave the impression first on Torque.
WordPress Agency